Bring Zero Trust to Your Data, Not Just Your Network
Confidencial enforces Zero Trust where it matters most - at the data layer.
Perimeters are dissolving. Networks are porous. Fire and identity checks aren't enough. Sensitive data leaks when files are shared, copied into AI systems, or stored in unsecured cloud folders.
Our platform embeds persistent encryption, access control, and auditability directly inside your files, even when they leave your environment.
What we protect
- Contracts, legal docs, source code
- R&D and IP
- PII and PHI
- Financial, HR, and operational files
You can’t trust the perimeter to protect your data
Despite advances in ZTNA and IAM, sensitive data continues to leak daily because traditional Zero Trust solutions typically stop at the network or identity level.
But what about...
What We Protect:
-
 Files shared with vendors or contractors?
Files shared with vendors or contractors?
-
 Documents pulled into AI workflows?
Documents pulled into AI workflows?
-
 Sensitive content sitting in public cloud folders?
Sensitive content sitting in public cloud folders?
-
 Unstructured data with no native enforcement?
Unstructured data with no native enforcement?
Without Zero Trust at the data layer, access controls break down.
80%
of enterprise data is unstructured & growing.60%
of breaches involve unstructured content.
63%
of sensitive files are shared externally, often without encryption or access restrictions.
How Confidencial enforces true data-centric Zero Trust
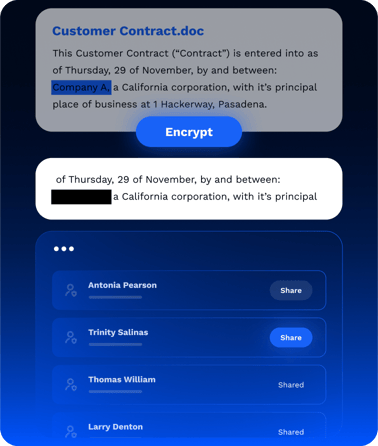
Confidencial embeds Zero Trust principles into the data itself, so protection follows the file, not the network. Whether it's shared externally, pulled into an LLM, or stored in cloud storage, our object-level encryption and policy enforcement ensure it’s only accessible to the intended users, agents, or models.
Platform Capabilities:
Object-Level
Encryption
Apply cryptographic protection inside documents (not just on the file), so access is granular, revocable, and traceable.
Granular
Access Control
Govern file access based on user, agent, model, department, or partner, with centralized rules that apply consistently across systems.
Secure
AI Enablement
Protect files before they’re fed into RAG or fine-tuning workflows, ensuring sensitive data is never ingested ungoverned.
Data Security
Posture Management
Get visibility into who has access to what data, where protection is missing, and how to reduce risk exposure fast.
Comprehensive
Audit Logging
Capture and log every file access, edit, share, or AI interaction for provable compliance and forensic readiness.
Persistent
Embedded Protection
Security policies and encryption travel with the data, whether it’s moved to the cloud, shared externally, or pulled into an AI model.
Zero Trust That Starts and Stays With Your Data
Knowing where your sensitive data lives isn’t enough. Confidencial takes it further, automatically applying the industry's first-ever data-level encryption based on labels, policies, or AI-powered discovery. Your data stays protected wherever it flows, even beyond your walls.
We secure the sensitive content buried inside contracts, legal agreements, medical records, R&D files, intellectual property, regulated data like PII, PHI, and HIPAA, as well as financial, HR, and operational documents.
Built-In Security for Every File, Everywhere It Goes
Confidencial embeds Zero Trust directly into your data, making every document self-protecting and policy-aware from the inside out.
- Replace file-based permissions with data-layer Zero Trust controls to enforce access policies across departments, regions, and devices
- Maintain control of sensitive data shared with third parties or used in AI workflows by applying persistent protection—even after the file leaves your environment
- Streamline audit prep and demonstrate compliance with frameworks like NIST CSF, CMMC, and ISO 42001 using automated policy enforcement and access logs
Business benefits
Confidencial helps you secure sensitive data, simplify compliance, and collaborate securely.
- Stronger Security Posture: Eliminate blind spots in file sharing, AI workflows, and data sprawl
- Prove Zero Trust Compliance: Align with ZTA mandates, privacy laws, and evolving AI governance frameworks
- Replace Legacy Controls: Go beyond folder permissions, DLP rules, or perimeter tools with true data-layer enforcement
- Reduce Insider & Third-Party Risk: Control who accesses sensitive content, even after it leaves your systems
- Simplify Audits: Full traceability, fewer tools, and automatic reporting

Watch Confidencial In Action

Ready to Zero Trust to your crown jewels?
See how Confidencial applies identity-aware protection and enforcement at the data layer to secure the sensitive content buried inside your documents.

FAQ
What does “Zero Trust at the data layer” mean?
It means applying Zero Trust principles—least privilege, continuous verification, and explicit access controls—directly to the data, not just the network or app layer. Confidencial enforces this by embedding encryption and access policies inside your sensitive documents.
How is Confidencial different from DLP or ZTNA?
DLP is reactive and often blocked by usability issues. ZTNA controls access to networks and apps, not the data itself. Confidencial embeds persistent, cryptographic controls into the files, so data stays protected, traceable, and governed, wherever it travels.
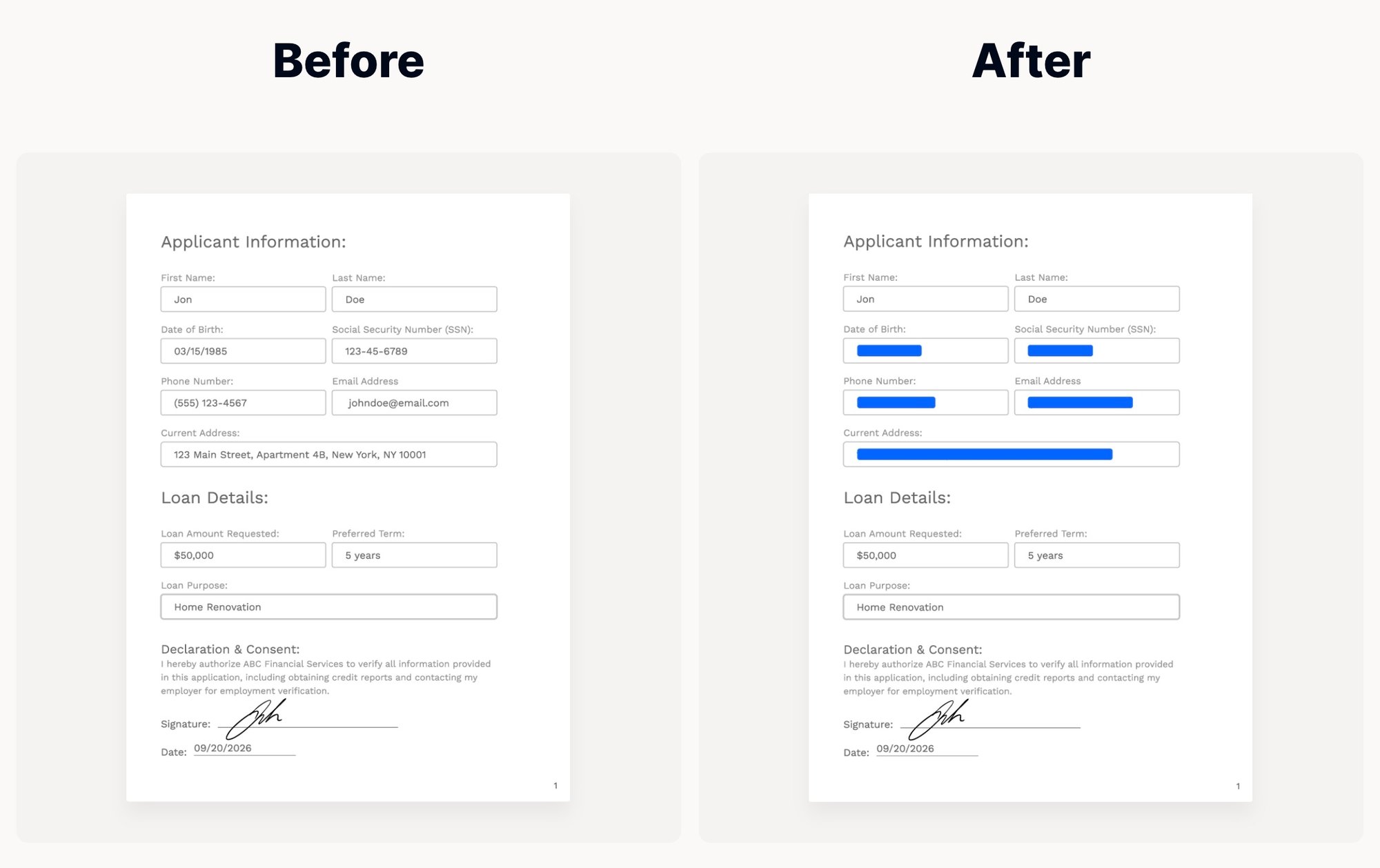
What is object-level encryption?
Granular encryption for specific elements inside a file—like names, SSNs, contract clauses—while preserving usability.
Does it integrate with my identity tools and cloud storage?
Yes. Confidencial integrates with identity providers and reads classification labels and access rules, so you can automate protection without reengineering your tech stack.
Can it protect data used in AI pipelines?
Absolutely. Confidencial is cloud-agnostic, AI-native, and built to protect sensitive data in any storage or AI environment - including RAG and fine-tuning pipelines.
